I am using a NetApp file server. Regarding this report, how should I simulate file permission settings and file activity behaviors to generate this report?
Hi, Cooper.
The suspicious admin activity report highlights instances where a user with a given level of access on a target resource ends up performing an operation that exceeds their effective access.
By its nature, this report highlights edge cases and suspicious behaviors, so producing resuts is always going to require a little creativity. Here is one such test plan involving the abuse of Backup Operators.
On your NetApp share, create a folder:
\\netapp01\Lab\Suspicious1
-
Set ACLs so your test user has Read-only (no Write/Delete).
-
Add the test user to the Backup Operators group, or grant SeBackupPrivilege/SeRestorePrivilege (Domain Admins already have this).
-
From a Windows client, open a command prompt as that user and run:
robocopy c:\temp \\netapp01\Lab\Suspicious1 test.txt /B(
/B= backup mode)
This will succeed even though the ACL snapshot says the user had only Read. -
Collect activity and run the report — it will show Activity = RW (mask 3) vs AllowedRights = 1 → flagged.
Hope this points you in the right direction!
-Ben.
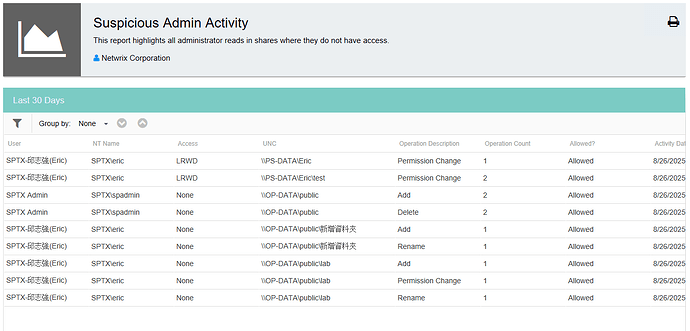
Please look at the screenshot. My public folder is set to allow domain users access, and users spadmin or Eric have domain admin privileges, so users should have permission to access the folder. The Suspicious Admin Activity results don’t seem to match the report description - is this correct?
Hi Cooper,
If you feel that the results you are receiving are inaccurate, please open a ticket with technical support at netwrix.com/support so that we may investigate this further.
This topic was automatically closed 60 days after the last reply. New replies are no longer allowed.