Attackers love service accounts. They’re rarely monitored, often over-permissioned, and almost never rotate credentials, yet they power everything from legacy scripts to AI agents. Netwrix Threat Manager 3.1 helps you identify and prioritize risk across these overlooked non-human identities while expanding detection for advanced persistence and privilege escalation techniques.
Want the full details? Click the link below!
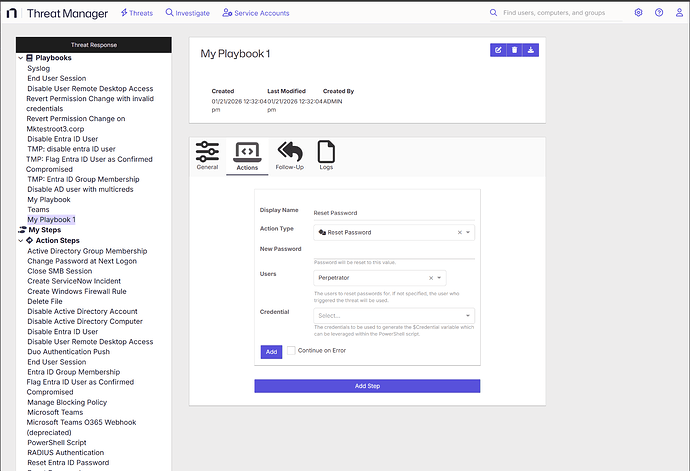
What’s Changed in Netwrix Threat Manager 3.1
Service Accounts Dashboard with ML-Based Discovery
The new dedicated service account dashboard gives you a centralized view to identify and prioritize risky service accounts, including those powering AI agents and automated workflows. It automatically flags stale or weakly encrypted accounts that attackers love to exploit. Built-in machine learning identifies service accounts by detecting pattern-based authentication behavior, feeding the dashboard with a complete picture of your service account risk.
This builds on existing detection capabilities, as Threat Manager has always monitored service accounts just like it monitors user accounts. What’s new is the ability to find them using Machine Learning and see their risk posture at a glance.
New Threat Detections
We’ve added specific detection rules to uncover subtle, advanced attack vectors:
- Primary Group ID Modification: Detects attempts to hide group memberships or escalate privileges by manipulating the primaryGroupID attribute.
- Potential BadSuccessor Abuse: Identifies abuse of the BadSuccessor attribute on AdminSDHolder—a stealthy persistence method used to re-infect protected groups.
- Suspicious DC Authentication: Flags anomalous authentication patterns involving Domain Controllers, helping detect rogue DC attacks or impersonation.
Netwrix Rebranding
The interface has been updated to align with Netwrix branding, ensuring a seamless, unified experience for security teams using multiple Netwrix products.
Bug Fixes and Miscellaneous Updates
- Playbook Execution History - Fixed user name missing on the history tab for playbook execution.
- Threat Detection Tool Coverage - Threat detection for Kerberoast attacks now properly identifies attacks performed with alternative tooling, closing detection gaps.
- Threat Rollup Time Configuration - Threat detection configurations include default rollup time values to ensure consistent threat aggregation behavior across all detections.
- External Authentication Provider Naming - Users can successfully rename external authentication providers without encountering errors.
- Multi-Value Field Export - Multi-value fields such as tags export correctly to CSV files with proper formatting instead of as object references, making exported data immediately usable.
- Investigation Attribute Access - Fixed the description for object renames.
- Custom Threat Deletion - Deleting custom threats properly removes associated job objects from alert query responses, preventing orphaned data.
- Investigation Logging - Investigation queries with verbose logging complete without encountering parsing errors that could interrupt analysis.
- Log Export Progress - Users see visual progress feedback when exporting large log files, improving transparency during long-running exports and preventing confusion about system responsiveness.
- Email Report Delivery - Scheduled reports deliver successfully via email without encountering subscription errors, ensuring reliable report distribution.
- Login Compatibility - Users can successfully log in even when very old cached data exists in their browser storage, preventing access issues after extended periods between logins.
- Installer Action Execution - The installer only executes post-installation actions when installation completes successfully, preventing errors during failed installations.
Need help with this update?
There are many different ways to get help with our products!
| Situation | Action |
|---|---|
| If you feel the product is broken and not working as intended… | Contact Support |
| If you have a question you’d like to ask other experts… | Create a discussion in the community: Threat Manager > Discussions & Questions |
| If you have a feature request… | Let our product team know directly: Threat Manager > Ideas |
| If you have something cool to show… | Show everyone what you built: Threat Manager > Show & Tell |
What are your thoughts?
We are always happy to hear from our users on what you like, and what you hope to see in the future. Please, share your thoughts below!